Imagine this: you’re in a coffee shop, and your buddy leans over to share a secret. But like, not just any secret. They whip out this ancient-looking letter and say, “This has a code that only we understand!” Pretty cool, right?
Well, this whole idea of secret messages goes way back. People have been encrypting letters for centuries, like spies in the movies. They’d use ciphers that sound fancy but are mostly just clever tricks to mix up letters and keep nosy eyes away.
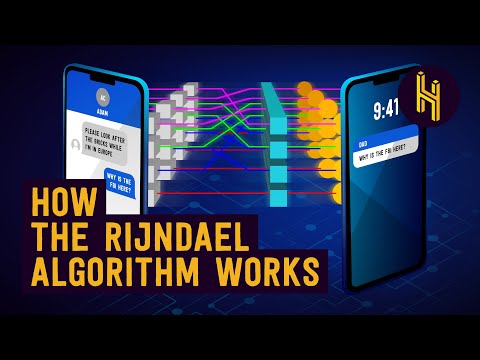
But what’s wild is how those old-school methods have evolved! Today’s encryption techniques are way more advanced. We’re talking about serious brainpower that keeps our digital conversations private.
So stick around! Let’s chat about some of the coolest innovations in letter encryption. Who knows? You might find yourself wanting to send secret notes again!
Exploring the Most Advanced Encryption Methods in Modern Science: A Comprehensive Guide
Encryption is a way to keep your secrets safe, like locking your diary. Imagine you’re writing a letter, but you don’t want just anyone reading it. That’s where encryption comes in! It scrambles your message into a code that only the person with the right key can read. Pretty cool, huh?
Now, let’s look at some of the most advanced encryption methods in use today. It’s like a secret club for techies, and everyone wants to get in!
- Symmetric Encryption: This is the classic method. Both the sender and receiver share a secret key to encrypt and decrypt messages. Think of it like a shared combination lock! An example is AES (Advanced Encryption Standard), which is widely used and super secure.
- Asymmetric Encryption: Here, things get more interesting! You have two keys: one public and one private. The public key can be shared with anyone, but you keep the private key to yourself. It’s kind of like giving someone an envelope that only you can open. RSA is a popular asymmetric algorithm.
- Homomorphic Encryption: This one’s mind-blowing! It allows computations on encrypted data without needing to decrypt it first. Imagine working on your math homework while keeping your answers locked away! It’s still being researched but shows promise for privacy-preserving data analysis.
- Quantum Encryption: Ever heard of quantum mechanics? Quantum encryption uses the strange rules of quantum physics to secure messages. One big player here is Quantum Key Distribution (QKD). If someone tries to intercept your message, it changes the content—you’ll know something’s up!
Now let’s add a human touch here—thinking back to when I was younger, I remember writing secret notes with my friends in school. We’d create codes that no teacher could crack! That thrill? That’s basically what encryption is about but on a much larger scale.
But wait—why should you care about all these fancy methods? Well, we live in times where protecting our information matters more than ever! With scams and hacks lurking around every corner, using strong encryption methods helps keep our personal stuff safe from prying eyes.
So there you have it! Encryption may sound like techy jargon, but it’s all about ensuring our secrets remain ours. When we communicate online or store sensitive information, knowing how these methods work can help us appreciate their importance even more. And who doesn’t love feeling secure when sharing thoughts or ideas?
Exploring the Substitution Cipher: The Science of Replacing Every Letter in Encryption
So, let’s chat about the substitution cipher. You know, it’s one of those classic methods of encryption where every letter in a message gets replaced by another letter. This might sound simple, but there’s a whole world of cleverness wrapped up in it!
The idea is that instead of sending your message as it is, you mix it up a little. Like, if you have the word “hello,” you might turn it into “ifmmp” by shifting each letter one spot forward in the alphabet. You get it? It’s like a secret code!
Now, this isn’t just child’s play. The substitution cipher’s been around for ages—think ancient Egyptians or Julius Caesar, who used what we now call the Caesar Cipher. He shifted letters a certain number of spaces down. Super cool for keeping messages safe back in the day!
- Alphabet Substitution: In this method, each letter can be replaced by any other letter. For example: A might become D and B could become G.
- Key: To decode the message later, you need to know the key—basically how the letters are swapped.
- Frequency Analysis: One way to crack these codes is to look at how often certain letters appear. Since some letters (like E and T) are used more than others in English, this gives away clues about substitutions.
This brings us to something really interesting: if someone knows how often certain letters show up in your message language—like maybe they see “X” popping up a lot—they can start figuring out what you’re saying! It’s like you’re letting them peek behind the curtain without meaning to!
You might think that just replacing each letter is enough to secure communication, but nope! Well-known methods came up later on that improved this approach because plain substitution ciphers are pretty easy to break when someone has time and patience.
The cool thing about today’s technology is that encryption has evolved from these simple methods to complex algorithms used across the internet! But remember where it all started? With simple substitutions! Just goes to show how something seemingly basic can lay down the foundation for more advanced techniques.
So why does learning about substitution ciphers matter? It gives you insight into how communication safety evolved over time. Next time you’re enjoying some secure messaging app, think back on those old-school ciphers that made it all possible!
Exploring the Three Key Methods of Encryption in Scientific Research and Data Security
Alright, let’s chat about encryption, particularly in the realm of scientific research and data security. It might sound technical, but it’s all about keeping important info safe and sound. You know how we lock our doors to keep our stuff secure? Well, encryption is like that—except in the digital world.
There are really three main methods of encryption that get talked about a lot. Each one has its own perks and quirks. Here we go:
- Symmetric Encryption: This method uses the same key for both locking and unlocking your data. Imagine you have a super-secret box and a key that opens it. You lock it up with one key, and to open it again, you use the same key! It’s quick and efficient but risky if someone gets their hands on that key.
- Asymmetric Encryption: This one’s a bit cooler because it uses two keys: a public key and a private key. Think of it like sending love letters. You can use anyone’s public key to lock your letter, but only the person with the matching private key can unlock it! It adds an extra layer of security, which is crucial when sharing sensitive scientific data.
- Hash Functions: Now this method is kind of different. Instead of locking up data with keys, hash functions take input—like a long string of text—and turn it into a fixed-length output. It’s like taking all that text and mixing it up into something completely different! If even one tiny thing changes in the original text, the hash changes dramatically too. This is super useful for verifying data integrity—like checking if your favorite recipe got altered.
You might wonder why scientists care so much about this stuff. Well, think about how often research leads to breakthroughs in medicine or technology. Keeping that information secure means protecting lives or innovations from falling into the wrong hands!
I remember once chatting with a researcher who had just made an exciting discovery related to cancer treatment. He was sharing notes on encrypted emails with his team across continents! He mentioned how knowing their conversations were safe allowed them to focus entirely on their work rather than worrying about prying eyes.
Encryption is essential for building trust in communications—it’s not just tech jargon; it’s real-world impact!
So whether it’s symmetric, asymmetric or hash functions at play, each method plays a critical role in ensuring our secrets stay just that—secret!
So, let’s talk about letter encryption. You know, it’s one of those things that sounds kinda old-school but is super important, especially in our digital age. I mean, think about all the personal stuff we send online—from texts to emails and even video calls. It’s like we’re living in a world where everyone could eavesdrop if they wanted to. Creepy, right?
I remember once sending a really private message to a friend during college. I hit send and then thought, “What if someone reads this?!” It was just a silly inside joke, but still! That moment stuck with me. It made me realize how vulnerable we can be when sharing information. So yeah, encryption is like putting your letters in a special vault that only you and the person you’re writing to can open.
Now, traditional methods of encryption were pretty basic but effective enough back in the day—like substituting letters or using simple codes. But as technology evolved, so did the need for more sophisticated methods. Enter modern encryption! It’s not just about keeping secrets anymore; it’s about protecting whole conversations.
One cool method that’s gaining traction lately involves something called **quantum encryption**. Sounds fancy, huh? Basically, it uses the laws of quantum physics to keep messages safe. It’s like sending a secret message that can’t be read without messing up the entire thing! That’s right—if someone tries to intercept it, the original message gets scrambled. Talk about next-level privacy!
And then there’s **homomorphic encryption**, which allows data to be processed while still encrypted. Picture this: you hand over your locked diary (or data), and someone can work on it without ever opening it up! How wild is that? This could totally change things for companies handling sensitive info.
But hey, with every innovation comes challenges too—like anyone trying to crack these codes might also get smarter over time. So it’s kinda like a never-ending cat-and-mouse game between those wanting privacy and those looking to invade it.
In the end though, remembering that we have options helps ease some anxiety surrounding secure communication! Whether it’s sending silly jokes or sharing serious responsibilities through an app or email – knowing there are innovative methods out there makes life just a bit more secure—and honestly less stressful too!