So, picture this: you wake up one morning, and your coffee maker is talking to you. Seriously! It starts asking about your plans for the day while brewing the perfect cup of joe. Sounds like something out of a sci-fi flick, huh? But it’s just a peek into the wacky world of cyborg anthropology. Yeah, that’s a thing! It’s not about robots taking over, but rather how we humans mesh with tech. You know how we’ve all got our smartphones glued to our hands? That kind of vibe—blurring the lines between what makes us human and what’s techy. And here’s the deal: this whole connection isn’t just interesting; it actually shapes our lives in ways we don’t always notice. Tech isn’t just gadgets anymore; it’s … Cyborg Anthropology at the Intersection of Humanity and TechRead more
Cybernetics
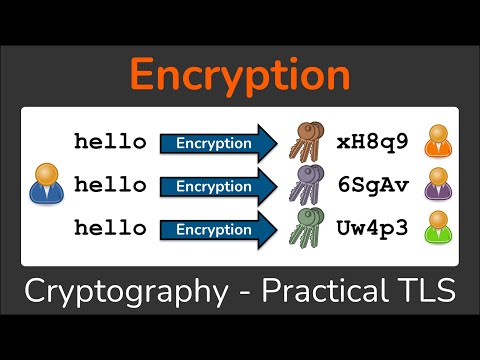
Cryptography and Security in Modern Scientific Research
You know, the first time I tried to send a secret message to my best friend in middle school, I thought I was being super sneaky. I used a simple code—A was 1, B was 2, and so on. Simple, right? Well, my plan backfired when she solved it in like five seconds! It got me thinking about how easy it is to crack codes when you don’t really know what you’re doing. Fast forward to today, and cryptography has come a long way from my childhood spy missions. Seriously, we’re talking about advanced algorithms that keep our secrets safe from hackers and nosey folks! In modern scientific research, this stuff is super crucial. Imagine all the groundbreaking discoveries happening behind encrypted doors; it’s like … Cryptography and Security in Modern Scientific ResearchRead more
Advancements in Military Cryptography and Its Science Applications
You know that feeling when you forget your phone password for the millionth time? Frustrating, right? Now, imagine if your life depended on keeping secrets and your code was crackable in seconds. Yikes! That’s where military cryptography comes into play. It’s like the secret sauce of security! Yeah, it keeps sensitive info locked up tighter than my grandma’s cookie jar. And honestly, it’s not just about spies and top-secret missions anymore. The crazy thing is that the advancements made in military cryptography are spilling over into everyday life and scientific applications. Think about how we communicate or share data! This stuff is literally everywhere, shaping modern tech without us even realizing it. So, get comfy while we dig into this world where codes and ciphers … Advancements in Military Cryptography and Its Science ApplicationsRead more
Symmetric Ciphers in Modern Cryptography and Data Security
Alright, picture this. You’re sitting at a coffee shop, sipping your latte, and you overhear someone chatting about how they just got hacked. Yikes, right? But here’s the kicker: they were using the same password for everything! Like, come on! So, what does this have to do with symmetric ciphers? Well, let me tell you. These little guys are like the secret agents of the digital world. They protect your data and keep those hackers at bay. In this digital jungle we live in, having a solid understanding of how symmetric ciphers work can be super handy. They’re not just some technical mumbo jumbo; they’re essential for keeping our secrets safe—think bank info or those embarrassing emails you hope nobody finds. So yeah, let’s chat … Symmetric Ciphers in Modern Cryptography and Data SecurityRead more
Advances in NSA Crypto and Its Role in Cybersecurity
So, picture this: you’re sitting at your favorite café, sipping a latte, and you see a guy in sunglasses typing away on his laptop. You can’t help but wonder, what kind of top-secret stuff is he working on? Maybe he’s cracking codes for the NSA or just ordering lunch. Who knows? But seriously, the world of cybersecurity is a lot like a high-stakes spy movie. There’s drama, there’s intrigue, and yeah—there are some super smart folks trying to stay one step ahead of the bad guys. And that’s where NSA crypto comes into play. These days, with everything being online—from our banking to our TikTok dances—keeping our data safe is like guarding the crown jewels. Advances in cryptography by the NSA are a big deal! … Advances in NSA Crypto and Its Role in CybersecurityRead more
Modern Cryptography and Its Role in Securing Data Today
Picture this: You’re trying to send a secret message to your best friend, but you accidentally send it to the whole group chat instead. Yikes, right? That’s kind of how important it is to keep our data safe these days. With everything from our bank info to cute selfies floating around online, keeping it secure is no joke. Seriously, who wants their embarrassing moments out there for the world to see? That’s where modern cryptography comes in like a superhero with a cape! It’s all about making your information unreadable for anyone who shouldn’t see it. So, let’s get into how this tech magic works and why it’s vital for our digital lives now more than ever. Exploring Real-World Applications of Cryptography in Science: A … Modern Cryptography and Its Role in Securing Data TodayRead more
Cipher Cryptography: Bridging Science and Secure Communication
So, you know how sometimes you feel like your texts are under surveillance? Like, is your buddy’s dog snooping on your chats? Okay, maybe that’s a stretch, but seriously, security in communication is kind of a big deal. Imagine sending a top-secret message. You’d want it to be as safe as a squirrel hiding its acorns. That’s where cipher cryptography comes into play. It’s like putting your message into a super cool puzzle that only the right person can solve. Back in the day, kings and spies were all about this stuff. They didn’t just send love letters without some fancy code! Can you picture them scribbling their secrets in a hidden language? How thrilling is that? In today’s world, we might not need to … Cipher Cryptography: Bridging Science and Secure CommunicationRead more
Bio Cybernetics: Bridging Biology and Technology for Progress
You know that moment when your phone autocorrects “I’m on my way” to “I’m on my way to the moon”? Makes you kinda wish for a super smart assistant that really understands you, right? Well, that’s sort of the vibe we’re talking about with bio cybernetics! It’s like this crazy mix of biology and technology. Imagine if your body could talk to machines and, like, they actually listened? Super cool stuff is happening in labs where scientists are blurring the lines between flesh and circuits. Seriously, we’re talking about creating tech that works hand-in-hand with our biology. It’s all about finding new ways to fix what’s broken or even making us better than we are now! So grab your snacks and settle in; this is … Bio Cybernetics: Bridging Biology and Technology for ProgressRead more
Innovations in NSA Cryptography and Their Scientific Implications
So, picture this: you’re at a party. Someone whispers a secret, and suddenly everyone’s ears perk up. Secrets are just so juicy, right? Well, that’s kinda how cryptography works, especially when we talk about NSA stuff. You know the National Security Agency? Those folks are like the ultimate secret keepers. They’ve got some seriously cool tech for scrambling messages so only the right people can read them. It’s not just about keeping snoopy spies at bay; it’s science with some huge implications! I mean, think about it: every time you send a message or make an online transaction, there’s this whole invisible world of algorithms working behind the scenes to protect your info. Sounds intense, huh? So let’s chat about how these innovations in NSA … Innovations in NSA Cryptography and Their Scientific ImplicationsRead more
Neural Cryptography: Bridging Science and Secure Communication
You know what’s funny? I once tried to explain cryptography to my grandma, and she thought I was talking about some kind of magic! Seriously, she imagined people in cloaks casting spells to protect secrets. Well, it turns out there is a bit of magic in the world of secure communication. Ever heard of neural cryptography? If not, don’t worry! It’s not all that complicated. Just imagine using the brainpower of computers to keep our messages safe. Sounds like a sci-fi flick, huh? The wild part is how it connects science with our everyday chats online. Yeah, those memes and selfies you’re sharing could be protected by some seriously clever tech that uses neural networks. Who knew our cute cat pictures could be tied to … Neural Cryptography: Bridging Science and Secure CommunicationRead more
Rubber Hose Cryptography and Its Role in Digital Privacy
So, picture this: you’re at a coffee shop, sipping your favorite brew, and you overhear two people talking about “rubber hose cryptography.” Sounds like something out of a detective novel, right? Well, it’s actually a pretty wild concept in the world of digital privacy. I mean, we’re all trying to be sneaky with our data these days. But what if someone could just use rubber hoses to get your secrets? Okay, okay, not literally! It’s more about the lengths some might go to extract information from you when encryption gets in the way. In a world where your online privacy feels like a game of hide and seek (and let’s be honest, sometimes it feels like we’re hiding while they seek!), understanding rubber hose cryptography … Rubber Hose Cryptography and Its Role in Digital PrivacyRead more
Cybernetics in Humans: Bridging Biology and Technology
You know that moment when your phone’s battery is dying, and you feel this sheer panic? It’s like your lifeline just slipped away! Well, what if I told you there’s a whole field where technology and biology dance together, kinda like a techy tango? Yeah, it’s called cybernetics. It sounds like something out of a sci-fi movie, right? But hold on. This stuff is real and can actually help us understand how humans interact with machines. Picture this: Your brain sending signals to your fingers to type out that perfect message. Now imagine if we could enhance that connection. Crazy thought, huh? Cybernetics is all about blending our biological selves with tech to make life a bit smoother—and sometimes even cooler! So let’s explore how … Cybernetics in Humans: Bridging Biology and TechnologyRead more
Advancements in Cryptography for Enhanced Network Security
So, here’s a funny thing I heard the other day. You know how we all have that one friend who’s super secretive? Like, they change their passwords every week and use weird phrases as security questions? Turns out that’s actually a great way to stay safe online! You see, cryptography is kind of like that friend but on steroids. It’s the magic behind keeping our digital lives safe from nosy hackers and malicious software. Sounds important, right? With all these advancements in technology, cryptography is evolving faster than you can say “data breach.” It’s fascinating how we’re getting better at protecting our information every day. Seriously, it’s like watching a superhero movie unfold in real life! So let’s chat about what’s new in the world … Advancements in Cryptography for Enhanced Network SecurityRead more
Innovations in Hybrid Cryptography for Secure Communication
Alright, so picture this: you’re sipping coffee in a café, trying to send an important message. Suddenly, you realize your Wi-Fi is about as safe as a kitten on a skateboard. Yikes! Now, what if I told you there’s this cool combo of cryptography that makes your messages way more secure? Seriously, it’s like having a secret decoder ring but for the digital age. Hybrid cryptography? It sounds all technical and fancy, but it’s basically the superhero of secure communication. Think of it as the perfect mix of two powerful forms of encryption working together like Batman and Robin. It’s pretty wild how this tech is changing the game. So let’s dive into why hybrid cryptography is where it’s at for keeping our conversations safe … Innovations in Hybrid Cryptography for Secure CommunicationRead more
Enhancing Security with PKI Cryptography in Science
You know that feeling when you’ve locked your phone, and you just can’t remember the password? Seriously, it’s like trying to solve a Rubik’s cube blindfolded. Frustrating, right? But here’s the thing. That little security drama is a sneak peek into a way bigger world: cryptography! Specifically, something called PKI, which stands for Public Key Infrastructure. Sounds fancy, eh? Well, this tech wizardry keeps our digital lives safe. You might not see it at first glance but trust me; it’s everywhere. It helps in science, banking, and even when you’re ordering pizza online. So let’s break down what PKI is all about and how it enhances security in the scientific community. You’ll see how this cryptographic magic works in a world where safety matters more … Enhancing Security with PKI Cryptography in ScienceRead more
HS256 in Cryptography and Its Role in Secure Communication
You ever try to send a top-secret message to a friend but ended up sending it to the wrong group chat? Yeah, that’s a bit of a nightmare, right? Imagine if your sensitive info got into the hands of, like, your ex or your boss. Yikes! Now, here’s where cryptography saves the day, kinda like superheroes but with code. HS256 is one of those secret weapons in digital communication. It’s like having a password on steroids that keeps your messages safe from prying eyes. So let’s chat about this cool little thing called HS256 and how it makes sure our online whispers stay just between us. You ready? Understanding the HS256 Encryption Algorithm: Applications and Implications in Modern Science So, let’s talk about **HS256**, which … HS256 in Cryptography and Its Role in Secure CommunicationRead more
The Role of Encryption Ciphers in Modern Science Communication
Okay, picture this. You’re hanging out with your friends, and someone gets a super-secret message on their phone. They’re all like, “What’s that?!” But they can’t tell you because it’s all scrambled up. Kinda cool, right? That’s how encryption ciphers work! Now, when you think about science communication, you probably don’t think about secret codes and spies. But encryption is actually a big deal in keeping information safe and sound. Imagine sharing your groundbreaking research findings without worrying they’ll get scooped or misused. Encryption ciphers are like those secret agents ensuring that only the right people get the info. It’s not just tech-y stuff; it’s real life! So let’s crack open how these clever little codes play a role in making sure scientific knowledge stays … The Role of Encryption Ciphers in Modern Science CommunicationRead more
Advancing Cloud Cyber Security Through Scientific Innovation
So, picture this: you’re chilling on the couch, scrolling through your phone. You check your bank account and boom! It’s like a horror movie—money’s gone! Just a random thought: how safe is your data up there in the cloud? Now, I get it. We trust the cloud with our photos, secret recipes, and even our life savings. But let’s be real; it’s kinda like leaving your front door wide open while you’re on vacation, right? Here’s where things get interesting. Scientists and tech geniuses are stepping up their game to beef up cloud security. They’re mixing science with tech to cook up some pretty wild solutions! Want to dive into this crazy mix of innovation and protection? Buckle up because we’re about to explore how … Advancing Cloud Cyber Security Through Scientific InnovationRead more
ElGamal Cryptography: Strengthening Digital Security Today
You know the feeling when you forget your phone at home and freak out a little? Like, how am I supposed to function without it? That’s kind of like what it’s like for our digital world—security is everything. And that’s where ElGamal cryptography struts in like a superhero. Imagine sending a secret message, and only the person you want can read it. That’s what ElGamal does, but in the tech world! It’s got this neat twist to keep prying eyes away from your info. Pretty cool, right? In today’s chat, we’re diving into how this whole thing works and why it matters now more than ever. So grab a coffee or whatever you’re into, and let’s get into this geeky treasure trove of digital security! … ElGamal Cryptography: Strengthening Digital Security TodayRead more
Advancements in Aes Gcm for Secure Data Transmission
You know that moment when you send a message and just hope no one’s peeking at your conversation? It’s a little nerve-wracking, right? Well, imagine if there was a superhero for your data. Seriously! A method that ensures your messages stay locked up tighter than a drum. That’s where AES-GCM comes into play. It’s like having an invisible shield around your digital secrets. This stuff is all about secure data transmission, and it’s making waves in the tech world. So let’s chat about how this fancy acronym can keep your info safe and sound while you’re out there sending memes or important info. Sound good? Evaluating the Security of AES-256 Encryption: Insights from Modern Cryptographic Research Alright, let’s get into the nitty-gritty of AES-256 encryption. … Advancements in Aes Gcm for Secure Data TransmissionRead more
Key Cryptography and Its Role in Modern Security Research
You know that feeling when you forget your phone password for the umpteenth time? Yeah, we’ve all been there. It’s that moment of sheer panic as you think of everything you’ve got locked away. Your photos, your messages—everything feels like it’s slipping through your fingers. But here’s the thing: cryptography is like the superhero of our digital world. Seriously! Without it, our secrets would be open for anyone to snatch. It’s what keeps hackers at bay and your Netflix account safe from nosy siblings! So, ever wondered how all this cryptographic magic works? Well, let’s take a little stroll through the fascinating landscape of key cryptography and see why it plays such a pivotal role in keeping us secure today. Exploring Key Cryptography: Its Integral … Key Cryptography and Its Role in Modern Security ResearchRead more
Private and Public Key Cryptography in Modern Security Systems
So, picture this: your friend texts you a super embarrassing secret, and you want to keep it safe. You wouldn’t just shout it out loud, right? You’d probably find a way to lock it up tight. That’s kind of how cryptography works—keeping secrets safe with some clever tricks. Now, there’s this thing called private and public key cryptography that’s like a magical duo for security. One key is yours alone; the other is for sharing with everyone else. It’s kinda wild when you think about it! Imagine being able to lock your treasure (or those silly secrets) while letting others use their own unique keys to unlock it. In today’s online world where breaches are as common as cat videos on the internet, understanding these … Private and Public Key Cryptography in Modern Security SystemsRead more
Public Encryption and Its Role in Scientific Communication
So, imagine this: you’re trying to send your friend a secret recipe for the world’s most amazing chocolate chip cookies. You write it all down, hit send, and—bam! It gets intercepted by your nosy neighbor who’s been eyeing your deliciousness. That’s kind of what scientists deal with when they’re sharing their groundbreaking ideas. Public encryption is like a digital lock for those super important messages. Seriously, it keeps prying eyes out while letting the right folks peek in. It’s a big deal in scientific communication and helps researchers share their findings without the risk of someone snatching them up. But why should you care? Well, when scientists get cozy with encryption, they can share without fear. That means faster discoveries and collaboration across the globe! … Public Encryption and Its Role in Scientific CommunicationRead more
The Role of Public Cryptography in Modern Science
So, here’s a fun thought. Imagine you’re sending a love letter in the mail. You know, the kind with doodles and all that mushy stuff? Now, what if I told you that there’s a secret code on it that only you and your crush can read? Sounds super sneaky, right? Well, that’s kind of how public cryptography works! It’s like having a magic key that only certain people can use to open messages or even keep your online banking safe. You might be wondering how this ties into science. I mean, scientists aren’t exactly known for their romantic letters. But seriously, when it comes to sharing data and research findings securely, cryptography is their best friend these days! Like, without it, everything we trust online … The Role of Public Cryptography in Modern ScienceRead more
Elevating Cybersecurity Engineering Through Scientific Innovation
Imagine this: you’re sitting in your favorite café, sipping on a latte, when suddenly your phone buzzes. It’s an alert that someone just tried to log into your bank account. Yikes! Your heart skips a beat, right? Well, that’s the kind of thing cybersecurity engineers are always thinking about. They’re like the superheroes of the digital world, constantly battling unseen villains trying to steal your data. But here’s the kicker: the tech we use to keep our information safe is changing faster than we can say “password123.” That’s where scientific innovation comes in. It’s not just about building better firewalls or smarter algorithms; it’s about thinking outside the box. So grab a snack and let’s chat about how science is making cybersecurity stronger and way … Elevating Cybersecurity Engineering Through Scientific InnovationRead more
Cybernetics and Its Role in Modern Scientific Innovation
You know that feeling when your phone seems to know what you’re thinking? Like you’re just casually talking about pizza, and suddenly, ads pop up everywhere? Seriously, it’s like your device is eavesdropping! Well, that’s kind of what cybernetics is all about. It’s this cool mix of science and technology that focuses on how systems communicate and control themselves. Think robots learning from their mistakes or smart homes adjusting to your favorite temperature without you lifting a finger. But here’s the kicker: it goes way beyond just gadgets. Cybernetics is actually shaking things up in fields like biology, psychology, and even economics! So stick around as we unravel how this quirky science is paving the way for modern innovation. Trust me; it’s a ride worth … Cybernetics and Its Role in Modern Scientific InnovationRead more