Alright, picture this. You’re sitting at a coffee shop, sipping your latte, and you overhear someone chatting about how they just got hacked. Yikes, right? But here’s the kicker: they were using the same password for everything! Like, come on!
So, what does this have to do with symmetric ciphers? Well, let me tell you. These little guys are like the secret agents of the digital world. They protect your data and keep those hackers at bay.
In this digital jungle we live in, having a solid understanding of how symmetric ciphers work can be super handy. They’re not just some technical mumbo jumbo; they’re essential for keeping our secrets safe—think bank info or those embarrassing emails you hope nobody finds.
So yeah, let’s chat about these cryptographic wonders and how they fit into the big picture of data security! You in?
Understanding Symmetric Ciphers: Key Concepts and Applications in Cryptography and Information Security
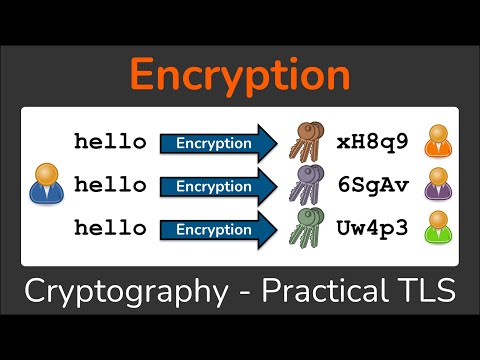
So, when we talk about symmetric ciphers, we’re diving into the world of cryptography, which is all about keeping our information safe and sound. Basically, symmetric ciphers use the same key for both encrypting and decrypting data. This means that the sender and receiver need to have access to the same secret key. Pretty neat, right?
Now, let’s break this down a bit more. Imagine you’ve got a message that you want to send to your friend without anyone else snooping on it. You take that message and mix it all up using a secret code (the key). Only you and your friend know how to unmix it, so outsiders can’t read it. That’s encryption in action!
But here’s the kicker: if someone else gets their hands on that key, they can also decrypt your message! So keeping that key secure is super important.
One popular example of symmetric encryption is AES (Advanced Encryption Standard). This has become a go-to method for securing everything from online banking transactions to personal messages. In AES, you can have key sizes of 128 bits, 192 bits, or 256 bits. The longer the key, the harder it is for someone to crack it.
Here are some key points about symmetric ciphers:
- Efficiency: Symmetric ciphers are usually faster than asymmetric ones because they use simpler mathematical operations.
- Key Distribution: The main challenge is distributing the secret key securely between parties without it being intercepted.
- Common Uses: You’ll find symmetrically encrypted data in things like VPNs (Virtual Private Networks) and file storage services.
Now let’s talk about those pesky risks involved. If one device gets compromised and the attacker finds out the secret key? Yikes! All communications secured by that key are exposed. That’s why many systems use a combination of symmetric and asymmetric encryption; they give you both speed and security.
Think of asymmetric encryption like handing someone a mailbox with two keys—one for locking (that everyone knows) and one for unlocking (that only one person has). You can drop messages in but only the person with the unlock key can read them.
The truth is this whole field is evolving continuously as we face new challenges in information security every day—from hackers trying to access sensitive data to countries trying to spy on each other.
In summary: understanding symmetric ciphers helps us appreciate how crucial secure communication really is in our digital lives today! It feels good knowing there are layers of protection out there keeping our secrets safe from prying eyes—even if it’s just a funny meme shared between friends!
Understanding AES 128: Exploring Its Symmetric Encryption Characteristics in Modern Science
So, AES 128, huh? This is a kind of encryption that’s super important in keeping our data safe. When you think about how much we rely on the internet—like banking, shopping, or just sending emails—you kinda realize how crucial this stuff is. Let’s break it down a bit.
First off, **AES** stands for **Advanced Encryption Standard**. It’s a symmetric encryption algorithm, which means the same key is used to both encrypt and decrypt data. Like if you had a magic box that locks with one key; you use that exact key to open it later. So if you lose that key? Yikes!
Now, when we say **128**, we’re talking about the size of the encryption key—specifically 128 bits. That might sound super technical, but basically it’s just a measure of how strong your lock is. The larger the number of bits in the key, the harder it is for someone to crack it.
Now let’s get into some characteristics of AES 128:
- Security Level: It’s considered quite secure for most applications today. Even though there are stronger versions like AES 256 (which uses a 256-bit key), AES 128 is still tough enough for everyday use.
- Speed: AES 128 is pretty fast compared to other encryption methods. If you’ve ever downloaded something and noticed it took less time than expected? Yeah, that could be partly because of AES!
- Simplicity: The structure of AES is relatively straightforward and doesn’t require crazy resources to run, which makes it suitable for all sorts of devices—from smartphones to cloud servers.
- Use Cases: You’ll find AES in everything from securing Wi-Fi connections to protecting sensitive information in financial institutions. Basically, if something needs locking up digitally? There’s a good chance they’re using AES.
Now here’s an interesting little story: I remember once trying to send an important job application through email. I was nervous about whether my personal info would remain safe while zooming through cyberspace. Guess what? My friend recommended using email services that employ AES encryption! Knowing my data was locked up with this tech gave me some peace of mind.
But with such power comes responsibility! While AES itself is solidly designed, like any tool, its security depends on how well you manage your keys. If someone gets their hands on your private key…well then all bets are off.
A lot has been said about quantum computers possibly cracking conventional encryptions in the future—but hey! For now, **AES 128** remains a go-to option for many businesses and individuals alike.
So there you have it—a little peek into what makes AES 128 tick! It’s like having a reliable vault for your digital treasures; as long as you keep your keys safe and secure!
Understanding Modern Symmetric Cryptography: Principles, Applications, and Advances in Computer Science
Alright, let’s chat about modern symmetric cryptography. This is a big deal in the world of data security and helps keep our information safe. You probably already use it without even realizing it!
So, what is symmetric cryptography? Well, it’s all about using the same key for both encrypting and decrypting data. Imagine you and your best friend have a secret language. Only you both know the words and how to use them—you share that knowledge with no one else. That’s kind of like how symmetric ciphers work.
Here are a few key points to keep in mind:
- Encryption and Decryption: When you send information, you transform it into a code using a secret key. The person on the other end uses that same key to change it back into something readable.
- Speed: Symmetric ciphers are generally faster than their asymmetric buddies because they do less complex math. They’re perfect for encrypting large amounts of data quickly.
- Security: The main challenge here is keeping that key secret. If someone gets their hands on it, they can read everything you’ve encrypted!
A classic example of this is the AES (Advanced Encryption Standard). It’s widely used by governments and businesses alike to secure sensitive information. Think military communications or even your online banking details!
Here’s a little story: Once, I was chatting with this tech-savvy friend who works in cybersecurity. He told me about an experience where his team discovered a vulnerability in an important application because someone had been careless with their keys—talk about heart-stopping! It really put into perspective how vital it is to manage encryption keys carefully.
Now let’s touch on some applications. Symmetric encryption isn’t just for secret messages! It can be found in:
- Email security: Protecting emails from prying eyes.
- File encryption: Keeping your documents safe on your computer or cloud storage.
- TLS (Transport Layer Security): Securing your web browsing experience so that hackers can’t steal personal info when you’re online shopping.
You might be thinking, “So what’s new?” Well, there have been some pretty cool advances lately! Research teams are constantly innovating better algorithms to boost security while maintaining speed. For instance, newer approaches focus on tackling the challenges posed by quantum computing—future-proofing our data like superhero-style!
The thing is, while we’re making all this progress, we need to stay aware of potential risks and challenges too. Cyber threats evolve constantly; if we get too comfortable with our current measures, things could slip through the cracks.
To wrap things up: modern symmetric cryptography plays an essential role in keeping our digital lives secure. The combination of speed and efficiency makes it indispensable in today’s high-tech world—seriously important stuff!
If there’s anything else on your mind regarding cryptography or anything science-y in general, just ask away!
Okay, so let’s chat a bit about symmetric ciphers. You know, those secret codes that help keep our data safe from prying eyes? It’s pretty wild how they work behind the scenes of our everyday life. When you send a message or make a purchase online, there’s a good chance some form of symmetric encryption is at play.
Picture this: I remember one time I sent a really important email to my friend about a surprise party. I was so paranoid that someone would snoop and ruin the surprise. So, I just put my trust in the email service’s security measures. This got me thinking about how much we rely on these technologies every day.
Symmetric ciphers are like having a key that opens a locked door to your secrets. The cool thing is that both the sender and receiver share this key for locking (encrypting) and unlocking (decrypting) the info. It’s like a secret handshake, but for computers! But here’s where it gets tricky: if someone else gets their hands on that key, well, it’s game over for your privacy!
Now, you might be wondering: why use symmetric encryption at all? Well, it’s super fast compared to its cousin, asymmetric encryption, which is kinda slower because it uses two different keys. And we all know speed matters when you’re streaming your favorite show or making online purchases.
That said, there’s still some risk involved with symmetric ciphers. If that key is weak or easily guessable—oh boy!—it could lead to some serious breaches in security. So companies invest tons of energy into making these keys strong and complex enough to withstand attacks from hackers who seem to have too much time on their hands!
And don’t even get me started on how crucial this tech has become in our digital age! With everything being online now—from health records to banking—it feels comforting knowing there’s some kind of protection out there.
In the end, while we may not think about them daily as we scroll through social media or shop online, these symmetric ciphers play an unsung role in keeping our data secure from harm. They’re like silent protectors in the world of bits and bytes—a little piece of technology that gives us peace of mind when sharing our lives in this vast digital universe!