So, you know how we all have those moments when we forget our passwords? It’s like your brain decides to take a vacation right when you need it most. Well, here’s the thing: there’s a whole world of cryptography that keeps our online lives secure.
One cool method? Elliptic curve encryption. Now, I know what you might be thinking—sounds like something straight out of a sci-fi movie, right? But it’s actually pretty down-to-earth and, dare I say, super smart.
Imagine sending messages that only your best friend can read. No hackers allowed! That’s what elliptic curves help us do—keep secrets safe without needing a supercomputer. It’s like having your own personal code language that even nosy people can’t crack.
Stick around; it’ll all make sense soon enough!
Exploring Elliptic Curve Cryptography: A Practical Example in Modern Cryptographic Science
So, elliptic curve cryptography (ECC), huh? It’s pretty cool—like math meets digital security. The whole point of ECC is to help keep information safe without needing massive amounts of computing power. It’s becoming super popular these days, especially with all our online transactions.
To get the gist of how it works, let’s think about curves. Imagine a graph where you have a smooth curve, sort of like an oval or a squished circle. That’s your elliptic curve. These curves are defined by some really specific mathematical equations, which may sound daunting but stick with me.
The essential magic happens when you think about points on this curve and how they relate to each other. Each point on the curve can be combined with another point in a way that creates yet another point on the same curve. This is called point addition. It’s like if you took two friends at the park who are also on their bikes—when they ride together, they create new fun paths along the way!
- Key generation: To start using ECC, you need a public and private key pair. Your private key is like your secret diary—only you should know it! The public key? It’s what you can share with everyone else; think of it as your address that people can use to send you messages.
- Encryption: When someone wants to send you a secure message, they take your public key and mix it with their message using some mathematics based on our elliptic curves. This makes sure only you can read it because only you have the secret decoder ring—the private key!
- Decryption: When the message arrives in your inbox (or however messages get to you these days), all you need to do is apply some more math magic using your private key to unveil what was sent.
You might be wondering why bother with this fancy encryption stuff. Well, there are cyber threats lurking around every corner! For instance, picture trying to access your bank account online without any protection—yikes! What ECC does is give us strong security against hacking attempts while keeping things fast and efficient.
An even cooler part? ECC uses smaller keys than traditional cryptographic methods but remains just as secure—or even more so! This means less data for devices to process and quicker transactions overall. Imagine sending money without waiting around forever for it to go through—sweet.
If you’re still scratching your head about what this all means practically: think about mobile devices or internet-of-things gadgets where resources are limited; ECC shines here because it allows them to stay secure without draining their batteries trying to do all that heavy lifting.
Wrapping up, elliptic curve cryptography is like having a superhero cape for digital communication—it makes sure our data stays safe from bad guys while being lightweight enough for everyday use. Pretty nifty stuff if you ask me!
Understanding Elliptic Curve Cryptography: A Comprehensive Example of Encryption and Decryption in Modern Science
Alright, let’s jump into the fascinating world of elliptic curve cryptography. You might be thinking, “What even is that?” Well, basically, it’s a way to keep our digital data safe. Imagine you’re sending a message to a friend and you don’t want anyone else to read it. That’s where encryption comes in.
So here’s the thing with elliptic curves: they’re not just for pretty math; they actually help in encrypting messages efficiently. Think of an elliptic curve like a smooth loop on a graph. It has some magical properties that allow us to make really hard-to-crack keys for encryption.
Encryption Process
1. **Generate Public and Private Keys**: First, each person involved generates two keys: a private key (which only they know) and a public key (which anyone can see). The public key is derived from the private key using the elliptic curve.
2. **Sending an Encrypted Message**: Let’s say Alice wants to send Bob a secret message. She takes Bob’s public key and uses it to encrypt her message. The cool part about this is that only Bob can decrypt it using his private key.
3. **Using Math**: Basically, Alice uses some mathematical operations involving points on the elliptic curve to scramble her message. This involves adding points together on that curve—sounds simple enough, right? But trust me, it gets complex under the hood!
Decryption Process
When Bob receives this encrypted jumbled message:
1. **Using His Private Key**: He uses his private key in conjunction with his own public key to unscramble or decrypt the message Alice sent him.
2. **Recovering the Original Message**: Through more calculations (that are super hard for anyone else to figure out), he ends up with the original text! Just like magic!
Now, you might be asking yourself why this matters? Well, think about how much we rely on online security these days—like banking or chatting with friends through apps! If no one could safely send messages or transfer money electronically without fear of prying eyes, our lives would be way more complicated.
Advantages of Elliptic Curve Cryptography
– It requires smaller keys than other methods (like RSA) while still being super secure.
– This means faster processing speeds, which is great for all those apps running on your phone.
– Its mathematics makes it incredibly tough for hackers trying to break in—seriously, we’re talking years of computing power!
In my mind’s eye, I picture those secret agents huddled around laptops trying their best to break codes while sipping their coffee! But thanks to methods like elliptic curve cryptography, many communications stay safe and sound.
So next time you’re sending sensitive info online—like your credit card number or even just an excited text about meeting up with friends—know there’s some pretty neat science behind keeping things secure! It’s wild how something so abstract ends up being so practical in our daily lives!
Understanding Elliptic Curve Cryptography: A Comprehensive Guide for Science and Technology
Okay, let’s chat about Elliptic Curve Cryptography (ECC). This is one of those topics that sounds super complex at first, but once you break it down, it makes a lot more sense. Basically, it’s a method of encrypting data to keep it secure. Think about how you lock up your diary or your favorite video game. ECC is like that, but a whole lot cooler.
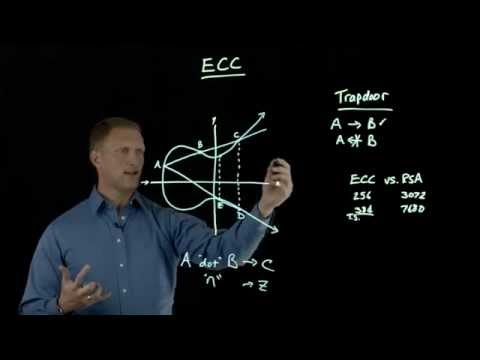
The fun part? ECC uses the mathematics of elliptic curves for encryption. Now, when I say “elliptic curve,” I’m not talking about some fancy shape you’d see in art class. Instead, it’s a specific type of mathematical curve defined by an equation. You know, something like y² = x³ + ax + b. It’s all about what numbers fit where on the graph.
Why should you care about all this? Well, ECC is super efficient compared to other methods out there—like RSA (that’s another encryption system). You see, with ECC, you can get the same level of security as RSA but with much smaller key sizes. That means faster computations and less storage space needed! Who doesn’t love that?
- Smaller keys: With ECC, you can use shorter keys while keeping your data safe. For example, a 256-bit key in ECC is believed to be as secure as a 3072-bit key in RSA.
- Speed: Because the keys are shorter and less computation is required, algorithms using ECC are typically faster than those using traditional methods.
- Battery life: If you’re thinking mobile devices here (smartphones and tablets), they benefit greatly from ECC because they consume less power while encrypting and decrypting data.
The process itself might seem daunting at first glance—don’t worry! Let’s break it down into bite-sized pieces. When someone wants to send you encrypted info using ECC:
- Your public key is created from your private key (a secret number). This public key can be shared freely without compromising security.
- The sender uses that public key to create an encrypted message.
- You use your private key to decrypt the message on your end.
This whole dance between public and private keys is what keeps everything locked up tight! It’s kind of like giving someone a puzzle box that only you have the right tool to open. Pretty neat if you ask me!
A practical example? Think about online shopping. When you buy something online (like those sweet new headphones), your payment info has to stay safe during transit. Websites use ECC to encrypt your sensitive data before sending it off through cyberspace so no one can peek at it while it’s flying around out there.
The emotional side of this tech? Imagine going through life always looking over your shoulder worried someone might snatch up your secrets or sensitive info—yikes! Thanks to advancements like Elliptic Curve Cryptography, we have ways to feel more secure when sharing our lives online.
If you’ve ever been curious about how safe things really are in our digital world, now you know that behind all those locks and keys are complex mathematical equations working tirelessly in the background!
You know, I was chatting with a friend the other day who’s like deep into cryptography. He started talking about elliptic curve encryption, and honestly, my eyes kind of glazed over at first. But then he broke it down in such an interesting way that I got hooked.
So here’s the deal: elliptic curve encryption is all about keeping your data safe online. Imagine sending a message to someone you really care about—like your best friend or that special someone. You wouldn’t want just anyone snooping on that, right? That’s where this fancy math comes into play.
Let’s picture this: you’re trying to send a secret message to your best bud using a lock and key. You’ve got the lock (which is basically a complex mathematical structure), and your friend has the only key that can unlock it. But here’s the cool thing—elliptic curves allow you to create super strong locks without needing huge keys! So, it saves space and makes things faster, which is super handy when we’re talking about smartphones and apps doing things on the fly.
Now, let me share something kind of personal that happened not too long ago. I was in a coffee shop working on some sensitive stuff for my job when I noticed someone behind me looking at my screen. It made me uncomfortable; what if they could see all my private information? It was then that I realized how vital these encryption methods are in keeping our conversations private.
What happens is that with elliptic curve encryption, even if someone intercepts your message while it’s flying through cyberspace, they’d need incredible computational power to crack it open—like trying to solve a Rubik’s cube blindfolded! It’s all about making sure only the right person gets to read what you’ve sent.
And here’s another thing: elliptic curves make digital signatures possible too. It’s like signing your name with a super secure stamp. This helps verify who sent a message without revealing any extra info—a bit like passing notes in class while making sure no one else can figure out who wrote them!
So yeah, next time you’re sharing something important online or using an app for banking or anything sensitive, just remember there’s some pretty neat math chillin’ behind the scenes keeping everything locked up tight! And honestly? Knowing all this makes me feel a little safer—and maybe even empowered—thinking about how we can keep our lives private amid all this tech—makes sense, huh?