You know what’s super funny? Most people think “SSH” is just a fancy way of telling you to shush! Like, you’re in a library or something. But here’s the deal: SSH stands for Secure Shell, and it’s got nothing to do with keeping quiet. It’s actually this cool way to make sure your online stuff is safe from prying eyes.
Picture this: you’re at your favorite coffee shop, sipping on that triple-shot caramel macchiato, and you decide to hop on the Wi-Fi. Uh-oh! You wouldn’t want anyone snooping around your files while you’re trying to check your emails, right? That’s where SSH comes in like a superhero with a cape made of encryption!
So, let’s chat about how these nifty SSH key exchanges work. They help establish secure connections so that your data travels safely through the digital jungle. Trust me; it’s definitely more exciting than it sounds!
Exploring PuTTY: Enhancing Scientific Research with Secure Remote Access Solutions
When scientists want to dive into their research from afar, tools like PuTTY can be incredibly useful. You might wonder, what’s the deal with PuTTY? It’s a handy application that lets you connect remotely to servers using something called SSH, which stands for Secure Shell. This is a protocol for secure communication over a network, and it keeps your data safe as it travels from one place to another.
Let’s break down some cool features that make PuTTY stand out:
- Secure Connections: SSH encrypts the data being sent back and forth. This means if someone tries to snoop on your connection—say a hacker—they’d just see gibberish instead of your precious research data.
- Authentication via SSH Keys: Instead of just using passwords—which can be weak—SSH allows you to use key pairs. That’s where you have a public key and a private key. The public key goes on the server, while you keep the private one safe. This makes it much harder for unauthorized users to access your data.
- Port Forwarding: With PuTTY, you can tunnel other types of traffic through your SSH connection. It’s like creating a secret passage that keeps everything else hidden from prying eyes! You could run database queries securely or even browse the web without showing what you’re doing.
- Session Management: If you’re hopping between projects, PuTTY lets you save all your settings per session. One click, and you’re right back in action!
You know, I remember helping my friend who was doing her PhD research on climate change models. She was collaborating with teams all over the world but worried about keeping her sensitive data secure while working remotely. Once we set up PuTTY with SSH keys for her project server access, she felt way more at ease knowing her information was protected.
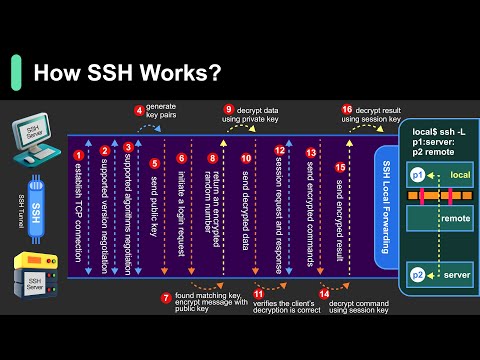
The mechanics behind SSH Key Exchange are pretty interesting too! Basically, when you attempt to connect using an SSH key pair, there’s an exchange process that happens before any encryption starts – this is known as the handshake process. During this handshake, both parties agree on how they’ll communicate securely using cryptography.
This exchange helps establish trust: if one side can prove that they possess the correct private key corresponding to what’s stored on the server (the public key), then they can establish a secure connection without exposing sensitive info like passwords.
Packing all these features into an easy-to-use interface makes PuTTY popular among researchers trying to protect their work while accessing remote servers efficiently. It’s amazing how technology provides such robust solutions for collaboration in our increasingly connected world!
If you’re diving into remote research or simply want peace of mind while accessing valuable information, tools like PuTTY are definitely worth checking out!
Enhancing Scientific Data Security: Understanding SSH Key Exchange Mechanics in Secure Connections
Alright, so let’s get into it! When we think about secure connections, especially in the world of data and science, one term that pops up a lot is SSH, which stands for Secure Shell. It’s like a secret passageway for your data, allowing you to connect to another computer safely. But how does this connection stay safe? Well, that’s where the magic of SSH key exchange comes in.
Basically, SSH uses something called cryptography. You might think of it as a code language. When two computers want to talk securely, they need to share a secret key without anyone else listening in. This is crucial because if someone were to eavesdrop, they could steal sensitive information or cause harm—like hacking your research data!
So how do the computers share this secret key? Here’s where the mechanics get a bit interesting. They use something called public and private keys. Imagine you have two keys for a lock: one is yours (private), and one you can give out to friends (public). You keep your private key safe and sound while sharing the public key with anyone who needs it.
Now let’s break down the actual process:
- Step One: The client sends its public key to the server.
- Step Two: The server uses that public key to encrypt a message containing a random number—it’s like a secret handshake!
- Step Three: The client then decrypts that message using its private key.
- Step Four: Now both sides have shared their “secret” number without actually sending it directly over the network.
This whole exchange means if someone tries to intercept the communication, all they get is some encrypted gibberish that’s useless. It’s kind of like passing notes in class where one person knows how to decode it and everyone else just sees scribbles!
Another cool point about SSH is that it’s not just for when you’re starting a session; it’s also used for maintaining security while you’re connected. Think about when you log into an online account; keeping everything secure during that session matters just as much as logging in safely.
Let’s say you’re working on an important project with colleagues around the world. You need to send them updates securely—nothing worse than having sensitive data leak out! Using SSH ensures that every communication stays protected through those layers of encryption we talked about earlier.
Now don’t forget about passwords! While SSH keys are super secure, using them alongside strong passwords adds another layer of protection—like having both locks on your door instead of just one.
In short, understanding SSH key exchange mechanics helps us ensure that our scientific data remains confidential and secure while being shared across networks. With technology advancing day by day, knowing these foundations can really help keep your work safe from prying eyes!
Understanding SSH Key Exchange Mechanics: A Scientific Exploration of Secure Connections
So, let’s talk about SSH Key Exchange Mechanics. It might sound a bit techy, but hang tight, and we’ll break it down together. So you know when you’re trying to keep your secrets safe? Well, secure connections are kind of like that. They protect your data from eavesdroppers while it travels across the internet.
At its core, SSH stands for Secure Shell, and it’s a protocol used to securely connect to servers. You can think of it like the digital version of sending messages in a locked box that only the intended recipient has the key to. Pretty neat, huh?
The magic happens during something called key exchange. This process is crucial because it helps two parties establish a secret that everyone else can’t snoop on. But how does this work? Let’s break it down:
- Public and Private Keys: Imagine you have two keys: one public and one private. The public key is shared with others, while your private key stays tucked away safely with you. When someone sends you a message encrypted with your public key, only your private key can unlock it.
- The Handshake: Here’s where things get interesting! When a connection starts, there’s this dance called a handshake happening between your computer and the server’s computer. They say hi and agree on which algorithms to use for encryption so they can securely send messages back and forth.
- D-H Key Exchange: Now things get even cooler with something called Diffie-Hellman (D-H) key exchange. Picture a secret meeting in which both parties create their own temporary keys that they don’t share publicly but use to help generate a shared secret key. This way, they can communicate secretly!
- Symmetric Encryption: Once they’ve agreed on that secret key through the handshake process, they switch gears from asymmetric encryption (using both keys) to symmetric encryption (using just one shared key). This means all their future chats get scrambled up in such a way that outsiders can’t read them.
You might be thinking: “That sounds complicated!” And you’re not wrong! But the beauty of it is that once it’s set up, everything happens automatically behind the scenes whenever you’re online—like magic! Just imagine logging into an online service without someone sneaking peeks at what you’re doing.
The real-world implication here is huge. We depend on secure connections every day: online banking transactions, shopping sites where we enter our credit card info—all these rely on SSH or similar protocols to keep our data safe. Without this techy wizardry going on behind the scenes, well… let’s say we’d be living in a much less secure digital world.
In summary, understanding how SSH key exchange mechanics work gives us insight into why we feel safe using technology today. It involves some high-level math and clever ideas about sharing secrets—sort of like how spies communicate in movies but much more accessible!
A little interesting note here: One evening after wrapping up an intense coding session myself, I realized how much I rely on these technologies just to chat with friends or share photos online without worrying about nosy neighbors peeking at my stuff! Seriously makes you appreciate tech when you think about what goes on under the hood!
If anything still feels unclear or if there’s something specific you’re curious about within this topic—just ask! Always happy to help unravel more science-y mysteries together.
So, let’s talk about SSH key exchange mechanics. It sounds super technical, right? You might be thinking it’s one of those heavy topics filled with jargon and complicated diagrams. But seriously, it’s like discovering how you and your friend pass secret notes without anyone else reading them — but way cooler because it’s all happening online.
A while back, I was trying to set up a secure connection for this little side project of mine. You know, just wanting to connect to my server without making it easy for someone sneaky to peek in. That’s when I stumbled upon SSH, which stands for Secure Shell. Basically, it’s a protocol used to securely manage computers over a network. Think of it as the online version of sending messages in a locked box that only you and your friend can open.
The magic really happens during the key exchange part. This is where the mechanics come into play. When you try to connect to your server using SSH, your computer and the server engage in this cool handshake dance – not literally dancing but you know what I mean! They share cryptographic keys that help verify each other’s identities.
But here’s where it gets interesting. Instead of just sharing one key openly (which would be like shouting your secrets across the playground), they use something called public and private keys. It’s kind of like having two unique keys: one is your public key that anyone can see, while the other is your private key that you keep secret, like hiding your diary under your bed.
When you initiate this connection, your computer sends its public key to the server. The server then uses its own private key to create a session that only both machines can understand—like speaking in code! It ensures that even if someone intercepts what they’re saying during their ‘dance,’ they won’t get anything useful because they don’t have access to those private keys.
I remember feeling pretty accomplished after figuring all this out! It felt like unlocking a new level in a game where my project would now be much safer from unwanted eyes watching my every move.
What really strikes me about SSH and these mechanics is how they’ve been built on principles of trust and verification—concepts we often take for granted in our daily lives too! Just think about friendships or partnerships; trust is vital for them too. There might be complex mathematics involved behind the scenes here with encryption algorithms and everything—but at its core, it’s all about keeping communication safe between trusted parties.
So yeah, next time you’re on some secure connection doing some serious business or just chilling with friends online, remember there’s a whole invisible world working hard behind the scenes to keep things secure through those clever SSH key exchanges! Isn’t technology amazing?